Articles and News
Most Vulnerable To Fraud, High-End Jewelers Must Balance Digital Marketing With Security | June 28, 2017 (1 comment)

New York, NY—One minute, jewelers are being lectured about the importance of digital marketing and the need for a constant social media presence if they want to stay relevant to tech-savvy consumers. The next, they're being warned not to say too much online because thieves are watching just as closely as customers. What's a jeweler to do?
Clearly, there must be a happy medium, not something easy to find in an era where technology changes almost daily and thieves make it their job to keep up with it, whereas hardworking storeowners have a lot of other things to do as well.
Last week news broke of a new widespread shipping scam in the industry, and both jewelers and suppliers—especially on the high end—were warned to be on the lookout for thieves impersonating trusted colleagues or customers to con jewelers and manufacturers into shipping merchandise that is then diverted to a different address than the original order. Retailers and manufacturers both are advised to take extra precautions before shipping any merchandise from telephone orders.
The Jewelers Security Alliance last week sent out a special bulletin about the scam. The reason it works so well is that the thieves do extensive research about the target company prior to placing a fraudulent order. Called social engineering, they scour the Internet for all possible details about the company by examining its social media posts, its website, and Google to get as much information as they can. Offline, they make repeated calls to the company to learn the names of its buyers, shipping department employees, managers, and what merchandise is available; often down to individual SKU numbers. In fact, it’s the telephone research that yields virtually all the information they need to strike, says John Kennedy, president of JSA.
When they do strike, they’re armed with enough information to successfully impersonate a credible retail customer of a supplier or, in the case of large chain retailers, the manager or an employee of another branch. In that case, the thief may request an item be transferred to the store they’re pretending to call from, and sometimes they’ll ask to have it sent directly to a “customer” or other non-store address.
Once the order is placed, the thieves then call the shipping company to have the package diverted from its original destination address given with the order to one they supply directly to the shipping company.
One of the variations of the scam is that a caller impersonating someone from a retail store contacts a supplier requesting that a high-end item be sent to the retail store. Sometimes the store has an existing account with the supplier and sometimes not, says JSA. Again, the goal of the impersonator is to divert the shipped package to a different address.
JSA recommended these procedures in its bulletin:
- Confirm whom you are really talking to. If it is someone from a retail store or even another branch of your own firm, and you do not know who you are talking to (or don’t recognize the voice), excuse yourself, saying you will call them back. Also call back the store after the order or request is made to confirm that both caller and order were legitimate.
- When you do call back, do not use the number given by the caller. Instead, call the actual number of the store, obtained through Google or elsewhere.
- Beware of calls from blocked or “unknown” numbers.
- Do not be fooled to give out inappropriate information to callers seeking information regarding your personnel or procedures. ALL EMPLOYEES MUST BE ALERTED NOT TO GIVE OUT INAPPROPRIATE INFORMATION. The scammers want to know as much as they can about your firm so they can sound legitimate.
- Strictly limit procedures allowing changes of address on shipments. Some firms have only one person who can authorize a change of address, or have specified to FedEx or other shipper that all attempts at changes of address should instead be returned to the firm shipping the goods.
- Firmly notify your shipper regarding your instructions concerning change of address.
JSA urges caution and restraint with what information you put online for your company. But in the age of social media and high-tech shopping, not having enough information online can make you seem like a dinosaur and send impatient customers elsewhere with a swipe or click, potentially never to return.
“Balancing the need for marketing and promotion in the digital age and the use of social media, and the need for security, is a difficult act. I think jewelers have to evaluate the level of risk they are willing to take based on their own circumstances,” Kennedy told The Centurion. But there are some absolute no-no’s regarding online info, Kennedy says:
- Information/and or pictures of your home, your kids (unless they are in the business), your travel plans, your daily routine of travel to the business (including route and times you leave and arrive), your car and license plate, restaurants, and other places you frequent.
- Be careful with video and/or 360-degree layouts of your store online to avoid virtual casing, he adds, and also be careful with names of your sales associates and employees online.
“This is just a brief sketch of an immensely complicated subject,” says Kennedy. “I would caution jewelers to err on the side of less information rather than more, and to be very cautious in their personal digital life.”
Jennifer Shaheen, president of White Plains, NY-based Technology Therapy, says the jewelry industry needs to change many of its policies if it’s going to compete effectively in today’s digital world—but that implementing some simple cyber-security best practices from other industries will work well to protect jewelers and suppliers.

Jennifer Shaheen
“The easiest thing to do is implement two-step verification," she says. One method is where the caller must give a cell phone number that’s already on file and you text a verification code to that number that they then have to supply to you. It’s almost foolproof because you can’t divert a cell text, Shaheen says. But the catch is that you must text the code only to a cell number that’s already on file with you, so make sure to get those numbers well before any potential transaction.
“Don’t do the transaction unless you have the cell number on file. Don’t trust the person on the phone, trust your files,” she says. If the caller tries to sidestep it by saying they just lost their cellphone, your response is, “I’m so sorry to hear that! Let me know when you have your new phone and I’ll text you the code.” Almost nobody changes their cell numbers anymore, Shaheen says, so that is an immediate red flag.
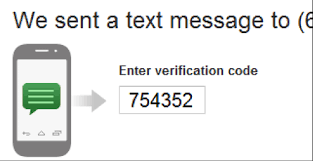
Two-step verification is the easiest protection against thieves impersonating a customer or fellow employee. Image: thatsnickq.com
Other two-step verification options include assigning passwords and/or PIN numbers to employees (for multi-store chains) or clients (for suppliers) and firmly instructing your employees that they are never to share any information about passwords, PINs or the process.
For general security, Shaheen agrees with Kennedy about the 360 video: it’s not a good idea, and it’s not necessary for marketing. Instead, a few well-positioned photos can tell your story without putting your security at risk, and things like Facebook Live can also help tell your story and provide authenticity for customers but preserve your security by carefully choosing the location and angle you film from.
As for whether or not to list your staff’s names online, Shaheen says it’s not that hard to get the information anyway. Since most people are on social media personally in some form—such as LinkedIn or Facebook—even if they’re not active, simply Googling the store or the employee’s name is eventually going to connect a would-be criminal to employees’ names and vice versa.
Finally, remember that email is not secure, so don’t send any sensitive information that way.
“Thieves are getting more and more creative, so we have to get more and more creative, but don’t penalize customers that are looking for information,” she says.
Read more about the industry shipping scam here and here. Read more about online jewelry fraud here.
Separately, but on a related note, if you suddenly notice that you don’t get mail you’re expecting (or a few days go by with no mail at all), immediately call your local post office to see if a temporary forwarding order has been placed. Because forwarding requests can be submitted online and don’t require identification proof of any kind, a common practice for identity thieves is to file a temporary change of address with the U.S. Postal Service, then apply for multiple credit cards in the victim’s name. The cards are applied for using the victim’s current address, and they’re shipped to that address, but then they’re held at the post office and forwarded to the phony address instead.
At minimum, check your credit every four months. Each of the three major credit bureaus—Experian, Equifax, and TransUnion—allows one free check per year. Use each one once, four months apart, to monitor your own credit, or consider signing up for a fraud protection service such as LifeLock or similar programs offered by Experian or AARP.
Finally, call your bank and credit card company before you travel so they know any charges you rack up on the trip are legitimate and you don’t find yourself in the train station in, say, Basel or Hong Kong, and your cards don’t work because they were flagged for unusual activity.